To complete the other networking activities, you will need to understand the “ping” command. It is one of the key tools when setting up networks. In essence, it allows you to check whether two systems can talk to each other. The names comes from active sonar, where a ping sound is send and an echo is received.
Ping is a command line tool and it is available on most systems. Options are different between the Windows and Linux tool. Common to all is the command ping and the ip address that is being pinged.
The tools sends a ICMP datagram to the host. The host sends the datagram back and the sender can determine the time the datagram took to propagate through the network. The command output reports the round trip time and any lost packets..
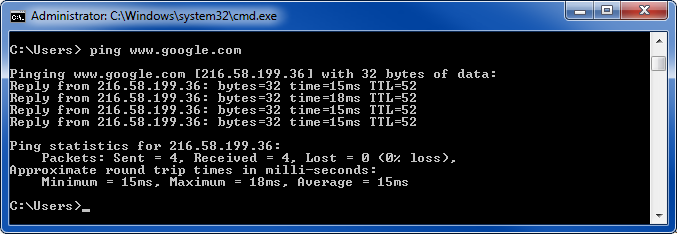
Below shows two examples of successful pings on Windows

Note that the tool reports the time that has elapsed between sending the packet and receiving the response.
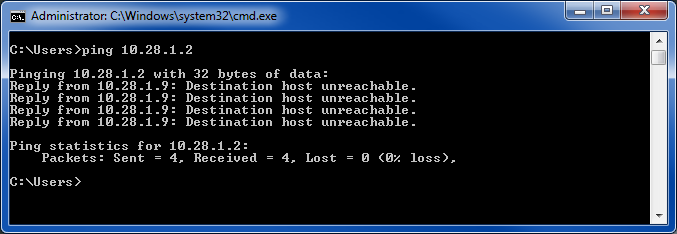
This examples shows an unsuccessful request.
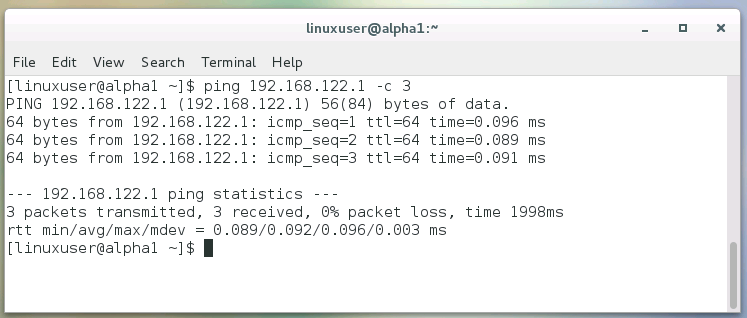
Under Linux the output looks similar. Note the -c 3 option. It limits the number of consecutive pings that are send.
So if somebody asks you whether you can ping host 192.168.4.3, simply type ping 192.168.4.3. If output shows round trip times, you can say yes. The destination host is reachable and the ping was successful.
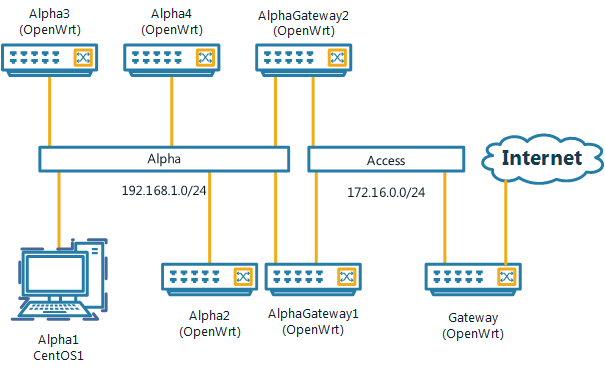
In this activity you have access to a CentOS Linux system. It is connected to two other nodes on the same network. The systems are named Alpha1 to Alpha3 and the network topology is depicted below.
IP addresses for nodes A1 and A2 are configured as shown below.
| Name | OS | Network | IP |
| Alpha1 | CentOS | Alpha (eth0) | 192.168.1.151/24 |
| Alpha2 | OpenWrt | Alpha (eth0) | 192.168.1.155/24 |
| Alpha3 | OpenWrt | Alpha (eth0) | 192.168.2.34/22 |
| AlphaGateway1 | OpenWrt | Not active | |
| AlphaGateway2 | OpenWrt | Alpha (eth0)
Access (eth1) |
192.168.1.1/24 (DHCP server)
172.16.0.190 |
You are required to configure node A1.
Now you should be able to use the ping command. Try the same activity on your own computer at home. Keep in mind that the IP addresses are different. You might want to complete the activity on IPv4 basics next.
Linux is a powerful operating system that is widely employed in server environments, as well as in embedded systems. This includes set-top boxes and the Android operating system, for example. It can also be used as a desktop environment and it supports similar functionality to Microsoft Windows.
Completing the activity, you will be able to compare graphical Linux applications with corresponding Windows applications.
Undertaking these activities students are required to maintain a lab book. Please see this post for more details: http://alexanderkist.com/keeping-a-lab-book/. All important steps and answers to the background research questions have to be logged. The documentation has to include enough information that another person can reproduce the results.
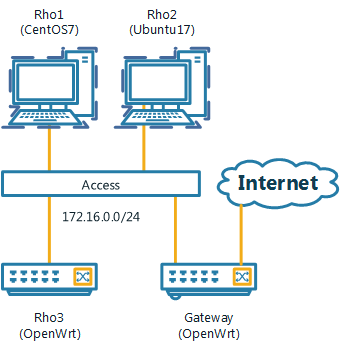
In this activity, you have access to a CentOS 7 Linux system (Rho1). It is connected to other nodes on the same network. However, for this exercise that is not important. The network topology is depicted below.
In the past, Linux installations were a tedious process, requiring detailed hardware understanding and advanced knowledge of Linux. Today, this process is as simple as installing software under Windows.
Linux comes in many flavours, called distributions. CentOS is used for this exercise. Main differences between the distributions include configuration, stability, release cycles, support cycles, ease of use and popularity. Ubuntu (www.ubuntu.com), for example, is another excellent distribution for general-purpose use. The popularity of distributions is changing over time. You can find a list of popular distributions here.
In this first activity, you will explore a graphical Linux interface. Linux provides software tools for almost any task. Standard office tools have been installed with CentOS. These are shown in the table below. Most of these applications are also available for Windows.
| Linux | Common Windows Tools | Available for Windows? | Online Alternatives |
| Firefox | Internet Explorer | Yes | Chrome |
| The GIMP | Photoshop | Yes | PIXLR |
| LibreOffice Writer | MS Word | Yes | Google Docs |
| LibreOffice Impress | MS PowerPoint | Yes | Google Slides |
| Thunderbird and Lightning | MS Outlook | Yes | Gmail |
Table 1: Linux Software and corresponding Windows Tools.
For each tool, open it, complete a few tasks and answer the following questions stating your personal opinion:
Firefox [1] is a web browser, widely used under Windows. You can access it by clicking on the blue/orange ball (earth with a re-fox) on the menu bar.
LibreOffice is an open-source, free opensource software suite that includes tools for many tasks, e.g. word processing, spreadsheets, presentations, graphics and databases. Write a short document and play with the options. Note that you can save MS Office compatible documents. Try also Impress and build a short presentation.
The GNU (General Public License) Image Manipulation Program (GIMP) is a free tool to retouch photos, compose and author images.
Thunderbird is mail and address book tool. Initially, you have to configure an email account. Evolution is an alternative email application.
There are a large number of free applications available that can assist with engineering problems. Many of these free applications are also available under MS Windows. Two examples include. GNUOctave and Scilab. Octave is a well-developed alternative to Matlab and it is installed on the test system.
The key learning objective of this activity is to develop a basic understanding of how IP addresses are setup for a single network. In the following activities we will extend this to multiple networks and the Internet. To complete the activity you will need to understand the ping command. It is one of the key tools when setting up networks. We have a Ping Activity that provides a introduction to the commend.
Background
IP addresses are 32 bit numbers that identify a network interface on a computer system. They written as 4 byte blocks separated by dot, e.g. 139.86.7.80. Public ip addresses are unique and are only allocated once worldwide. All devices that are connected to the Internet will have an IP address, either IP Version 4 or IP Version 6. In this activity we will cover IPv4.
In this activity you have access to a CentOS Linux system. It is connected to four other nodes on the same network. The systems are named Alpha1 to Alpha4 and Alpha Gateway1. The network topology is depicted below.
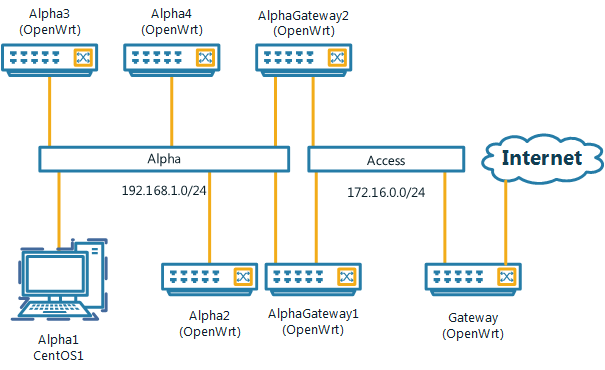
IP addresses for nodes are configured as shown below.
| Name | OS | Network | IP |
| Alpha1 | CentOS | Alpha (eth0) | 192.168.1.151/24 |
| Alpha2 | OpenWrt | Alpha (eth0) | 192.168.1.155/24 |
| Alpha3 | OpenWrt | Alpha (eth0) | 192.168.2.34/22 |
| AlphaGateway1 | OpenWrt | Alpha (eth0)
Access (eth1) |
192.168.1.1/24
172.16.0.145/24 |
You are required to configure node A1.
To communicate between two systems on the Internet, an IP packet needs to be forwarded from one system to another. This will involve a process of routing and forwarding of packets.
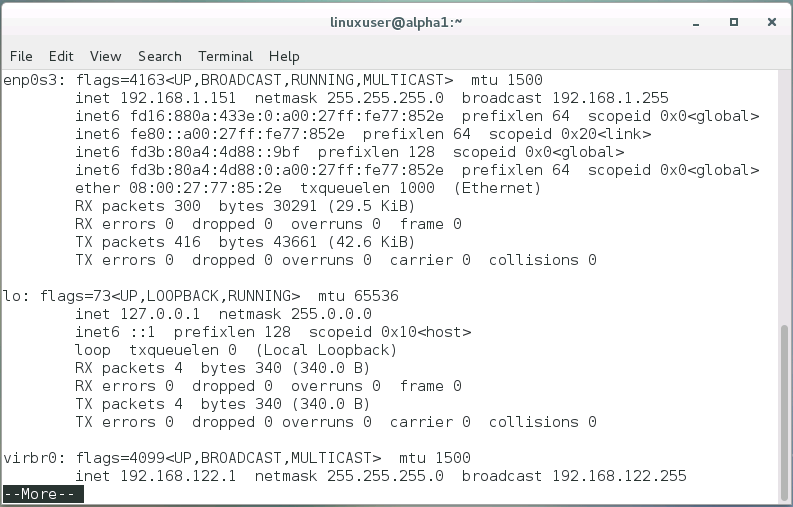
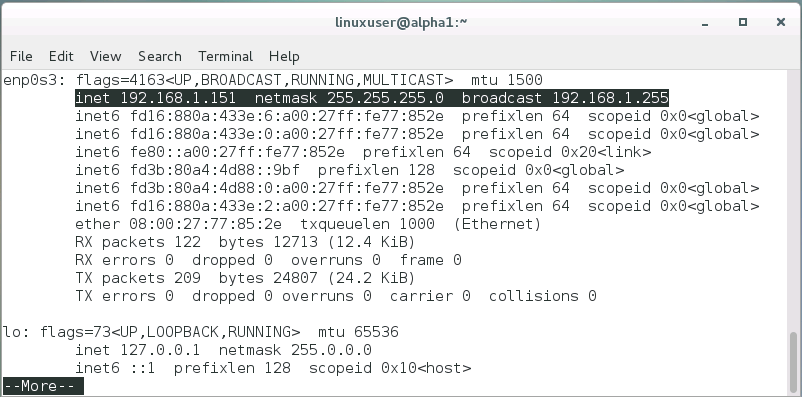
In the simplest case, one program communicates with another program on the same computer. This is done via the loopback interface. This is a virtual interface and it is located at IP address 127.0.0.1. To show the show the local network interface you can use the ifconfig command.
The command will show a number of interfaces:
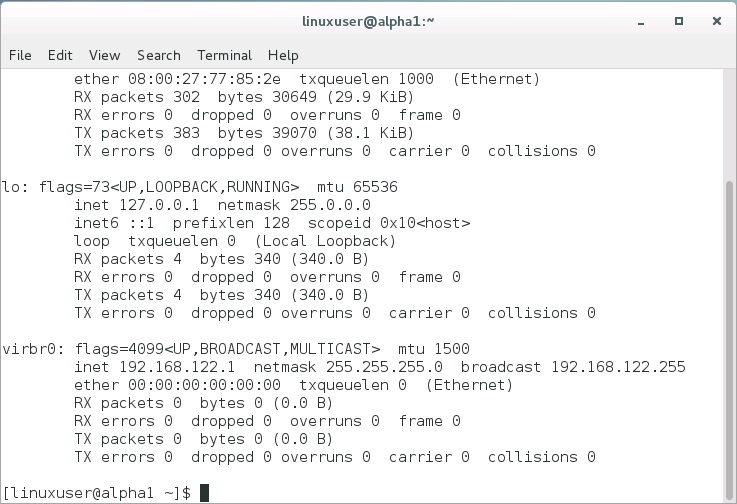
At this point we are interested in the loopback interface lo. It shows an internet address (inet) of 127.0.0.1 and a network mask of 255.0.0.0. We will discuss network masks in a moment. For now you can see whether you can ping the local interface.
If an IP address is located on another system, there are generally two options. Both systems are connected to the same of different networks. Systems that are located on the same network are reachable on the link layer, e.g. they are on the same Ethernet network. This means that the local networking stack can send packets directly to the destination node.
An IP address by itself does not specify a network. That is where the network mask comes into play. It divides the 32 bit IP address into a network and a host portion by specify the mask bits. This become more obvious if network masks are written in binary format. A network mask of 255.0.0.0 becomes 1111 1111 . 0000 0000. 0000 0000 . 0000 0000. (We have added spaces to make it more readable). Doing a logical bitwise AND of an IP address and this network mask will yield the first byte of the address with all other bits zero. This is the network address. Two IP addresses are on the same network if the have the same network address.
An alternative notation that is widely used identified the number of bits that makeup the network address, e.g. 127.0.0.1/8. Both mean the same.
After booting up, A1 has no IP address preconfigured and there is no DHCP server active on the network. Doing ifconfig, the information about the first interface, scrolled off the screen. You can either press shift and the page-up keys to scroll up, alternatively you can use the more command.
To change to the next screen, simply press the spacebar. You can now see the information for the first interface:
Ways how to set IP addresses differ between distributions. Here we will use the GUI utility.
You will get a popup window like this:
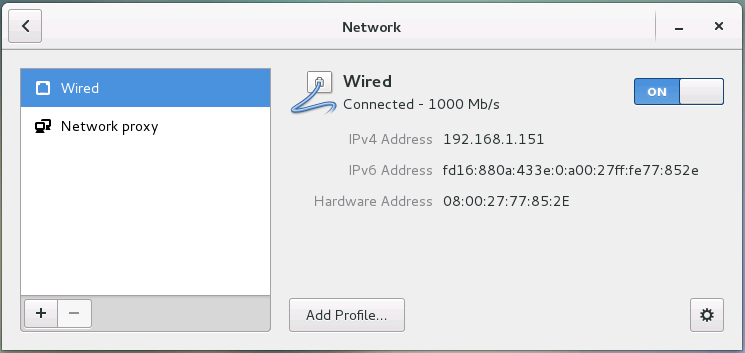
Now you can enter the IP address and network mask for host Alpha1. The notation ip address/24 implies a network mask of 255.255.255.0 See the table above for details and leave the Gateway field blank. Click Apply to save the changes. To activate the changes, you have to turn the Wired adapter off and on again. Close the window.
Now you can reach the other host on this subnet.
You are not able to reach Alpha 3. Our current network address is 192.168.1.0. The network address of Alpha 3 is 192.168.2.0 using our network mask of 255.255.255.0. You might have noticed that Alpha has a different number of bit allocated to the network address: /22. This means the network mask is 255.255.252.0. In binary notation the third byte is 11111100. If we use this mask with Alpha 3, the network address is 192.168.0.0. If we do it with Alpha1, we get the same network address. Changing the subnet mask of our host Alpha1 to 255.255.252.0 should allow us to ping host Alpha3. Let’s try it.
Did it work? If not did you turn the network off and on?
Configuring an IP address and network mask on a local interface allows you to reach hosts on you subnet. How do you reach hosts that are not directly connected to you? That’s where the default gateway parameter comes in. The default gateway is where a system sends packets if it can’t deliver them on the local network. In our case that is Alpha Gateway1. Go back into the IPv4 configuration and add the IP for the gateway: 192.168.1.1. Now you are able to reach the gateway of the next upstream node 172.16.0.1. Make sure that it is working using ping and don’t forget to restart the network interface after you made the changes.
This has been a very basic introduction. Why not try the activity with two computers at home? All you need is two computers that are connected to a common network, either wirelessly or wired.
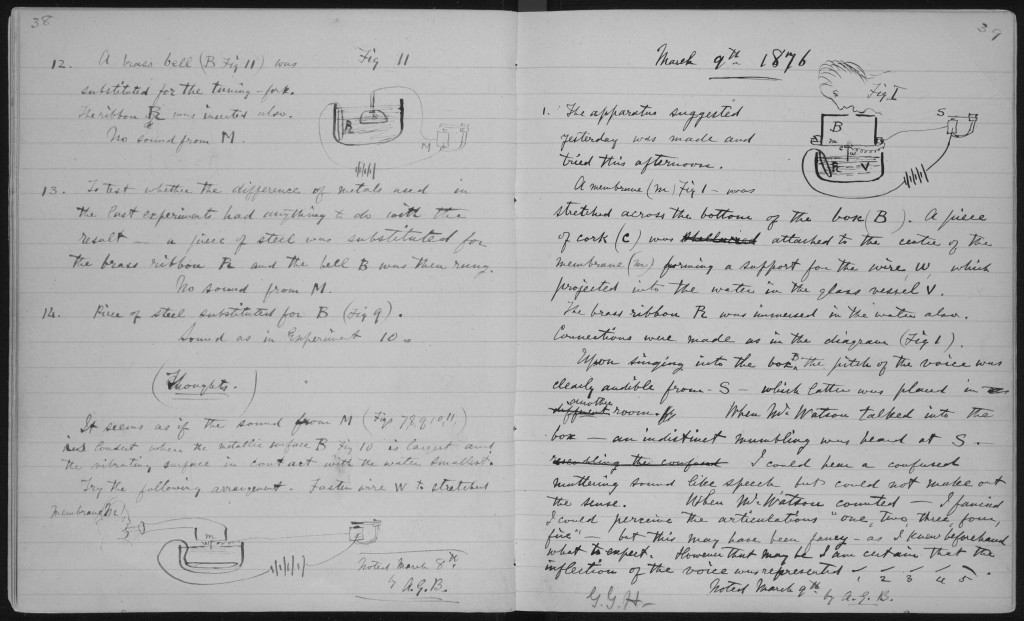
It is important to document your work and keep a record of the environment, your decisions, settings, observations and results.
If you are undertaking research, a lab book (or laboratory book) has a formal roll as a record of your activities and it can be a record of your contributions to a project or your inventions. As such a formal lab book is usually bound with numbered pages. Entries are dated and made permanently, i.e. using a ballpoint pen rather then a pencil. The log is usually written on the spot. The record includes the experimental set-up, collected data, observations and initial insights. It has to include enough information that another scientist can reproduce the experiment.
Lab books or work log books have also a roll in normal engineering practice, e.g. during development and commissioning. While the requirements might not be as rigid, it is important to keep a record of completed tasks, settings, issues encountered, etc. As above, the aim is that the lab book or log include enough information for another person to reproduce decisions or to continue the work. It also serves as an archive for the book keeper themselves. Thing that are obvious right now might not be as clear in a couple of month, or years.
The short answer is – it depends. What is the purpose of the log book? Are you documenting the work for your self, for colleagues, or for regulatory or legal reasons? The document has to include enough information that somebody else could take over and continue the activity at any time. In other words, using the original documentation and your lab book, somebody at a similar skill level should be able to reproduce your work.
For the purpose of practice activities in our courses, it has to include:
For the practice activities, you are welcome to maintain an electronic lab book. Make sure you save it somewhere you can access it easily each week.